One Deal, One Deadline: Inside a Ransomware Negotiation Ultimatum
When ransomware hits, the first messages exchanged often sound almost polite. But behind that calm tone sits a mix of fear, control, and desperation. The leaked conversation between a victim company and the ransomware group shows what those talks really look like and how cybercriminals use pressure, deadlines, and carefully worded threats to keep victims engaged.
The Opening Pitch
The conversation starts with a short and direct message from the attacker:
“Hello. I’m here. How can I assist you?”
It’s strange to see “assist” used by someone who just took down an entire network. But this is how most ransomware groups talk calm, professional, and transactional. They want victims to think of this as a business deal, not a crime.
Soon after, Qilin makes the situation clear:
“Your company’s network is attacked and the entire system is encrypted. We have downloaded all the company’s confidential data.”
Then comes the list of what the victim gets if they pay a “package” of promises:
- A decryption tool for all devices
- A list of files taken from the network
- Proof of data deletion
- A report on how they got in
- Security recommendations
- A promise not to attack again
- A “guarantee” they will forget the incident
The list is detailed and oddly methodical, like an IT service contract. This approach is intentional. Attackers want to project control and reliability, even while holding the company hostage.
Testing the Deal
The victim plays along, asking for proof that Qilin actually has the stolen files. The attacker sends small samples and offers to decrypt a few test files as evidence that their tool works. They even warn the victim not to send “valuable information” in those test files.
That tone, part professional, part manipulative runs through the entire chat. Every message is designed to make the victim feel like cooperation is the only rational choice.
Negotiation Begins
Once the victim confirms that the decryptions work, they try to negotiate:
“We are considering your demands. Is there any way you could provide a discount to your price?”
Qilin quickly replies with a token gesture:
“As a sign of goodwill and quick closing of the deal, we are ready to give a 10% discount.”
They drop the ransom to $63,000. The number itself is less important than what it represents a chance for Qilin to show “flexibility” while still keeping control.
But when the victim asks if they can pay only for part of the deal specifically, to have their data deleted without decrypting anything the tone changes sharply. Qilin responds:
“Understand that we don’t have something that requires you to pay separately. Any payment includes all our terms and conditions. It’s one package. Take it or leave it.”
This is a key moment. The victim is trying to limit damage and cut costs, but Qilin refuses to split the offer. They insist on one bundle: pay for everything or get nothing. It’s not negotiation, it’s control disguised as structure.
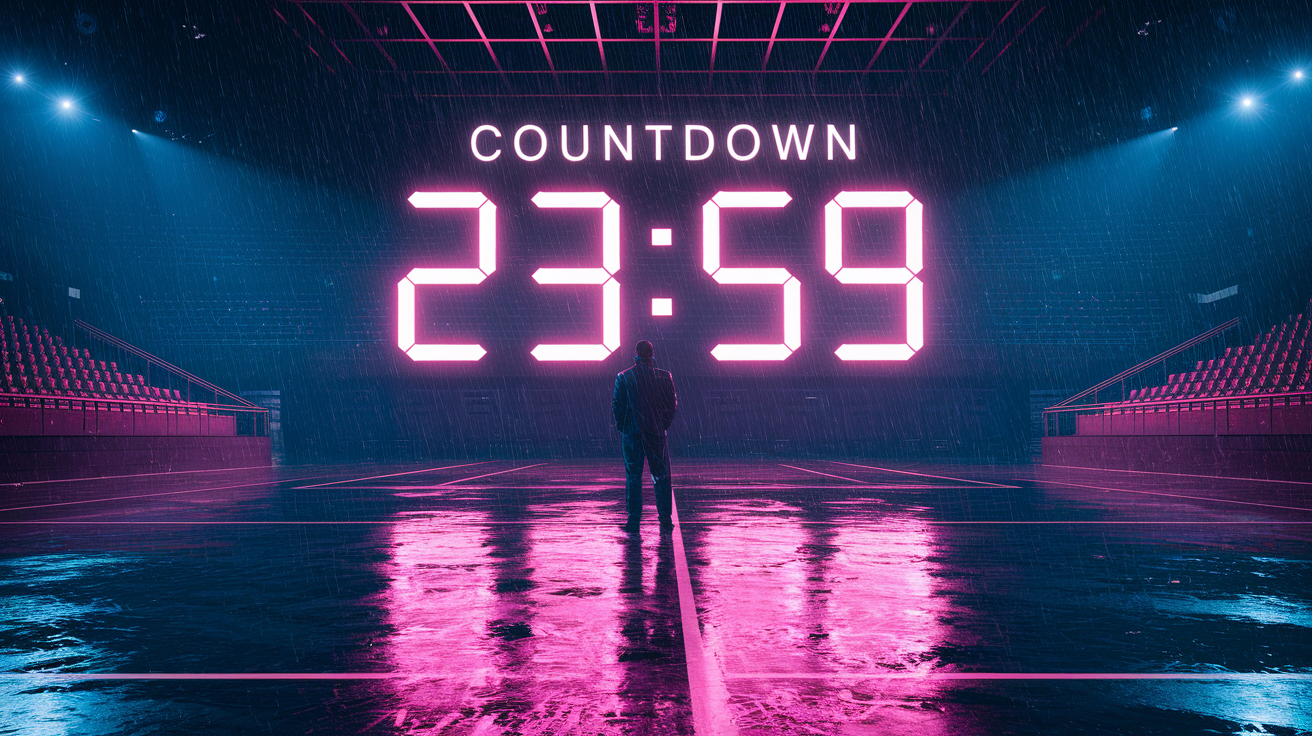
The Timer Tactic
As the chat continues, Qilin introduces another common tactic: the timer. They set a deadline for payment and link it directly to public exposure.
“We see that you are interested in making a deal as soon as possible, so we do for you an exception and extend the timer till the 19th of February.”
And then the threat:
“Please, don’t delay with it, otherwise we will return with the tools which are stronger. You must understand that as the timer will expire we will post your files on our blog.”
The mention of “our blog” isn’t casual. Many ransomware groups maintain public leak sites on the dark web where they post stolen data if victims refuse to pay. The timer becomes a psychological weapon, it forces victims to act under pressure while the attackers appear to be “fair” by granting small extensions.
The victim, still waiting for internal approval, asks for another day. Qilin agrees but makes sure to reinforce the urgency:
“We extended the timer for 24 hours.”
Playing on Fear
After the deadline extension, Qilin tries one more push. They lower the price again to $60,000, calling it a “very good discount.” But the tone hardens. They accuse the company of ignoring the safety of its patients:
“We see that you are not interested in the security of your patients and choose to play the silent way. Tomorrow we will publish a press release about you on our blog.”
This mix of threat and guilt is calculated. By mentioning “patients,” Qilin implies the victim is a healthcare organization and that exposure could cause real harm beyond financial loss. It’s emotional manipulation dressed as urgency.
The message ends with a dark promise: if payment doesn’t arrive soon, all of the company’s data will be made public.
The Business of Extortion
What stands out in this negotiation isn’t just the threats. It’s the tone. Qilin’s representatives write like customer service agents following a script. They’re polite, even respectful, but every line is designed to trap the victim in a limited set of options.
They offer “discounts,” “extensions,” and “assurances” all things you’d expect in normal business communication. But none of it means anything. Once a company pays, there’s no real guarantee that the attackers will delete anything or walk away for good.
When Qilin says, “You will get everything you agreed on,” what they mean is, “You might get what we decide to give you.”
Why It Matters
This transcript highlights the reality of modern ransomware. It’s not about random chaos or quick hits anymore. It’s structured crime that mimics professional negotiation. Attackers understand human psychology - they know how to appear reasonable while applying pressure.
The timer on the attacker’s blog, the “one package” rule, and the calm tone are all part of a method. Every message is a step toward making payment feel like the only logical move.
For defenders and IT teams, the lesson is clear: these negotiations aren’t just technical events; they’re human interactions shaped by stress and fear. Training and preparation matter just as much as backups and patches.
Conclusion
This negotiation is more than just a record of a cyberattack, it’s a look at how modern extortion works in real time. Every sentence is crafted to keep the victim off balance, promising help while tightening control. The mention of the timer and the threat to post stolen data on their blog show how attackers blend urgency and fear to force decisions.
When the victim asked for a “delete data only” package, Qilin’s response: “It’s one package. Take it or leave it.” said everything about who held the power. The attackers set the terms, controlled the clock, and dictated the tone.
Ransomware today is about negotiation as much as intrusion, with criminals leveraging pressure, timing, and psychology alongside technical breaches to maximize payouts.
For organizations, this highlights why response planning matters. It’s not enough to have backups or cybersecurity insurance, teams need to know how to handle the human side of an attack: how to communicate, when to engage, and when to walk away.
The Qilin case is a reminder that behind every encryption key and data leak post, there are real people on both sides of the screen: one trying to buy time, the other selling it back at a high price. And as long as ransomware remains profitable, these “conversations” will keep happening, each one starting the same way:
“Hello. I’m here. How can I assist you?”
Full Transcript
FULL TRANSCRIPT:
Attacker: Hello. I'm here. How can I assist you?
Victim: Hello?
Attacker: Your company's network is attacked and the entire system is encrypted. We have downloaded all the company's confidential data. After payment you will receive.
1. Decryption tool for all devices
2. Complete list of files taken from the network.
3. Proof that all your data has been deleted.
4. Information about how we got into the network.
5. Security recommendations to stop future attacks.
6. Promise that we will not attack you again in the future.
7. Guarantee that we will forget about this incident.
Victim: ok, what do we need to do?
Attacker: We will provide the list of files what we took from you as soon as possible and you can offer 3 names of files from it and we will provide them as a proof of availability. Also you can send 3 encrypted files and we will decrypt them as a proof that our decryption tool really works. But these files must not contain a valuable information.
Attacker: file tree.txt (0.232 MB)
Victim: Thank you, I'll review and pick out some files
Victim: Please provide us with copies of the following files:
- [redacted].xls
- [redacted].pdf
- [redacted].docx
Attacker: We will do it as soon as possible.
Attacker: [redacted].docx (0.032 MB)
Attacker: [redacted].xls (0.039 MB)
Attacker: [redacted].pdf (0.484 MB)
Victim: ok, so next I'm suposed to send you encrypted files? How am I supposed to get to those when you've encrypted the server?
Attacker: In order for you to make sure that we can really help you decrypt all your files and prevent all your information from going online - you can offer us some test files ... and we will decrypt them. After full payment you will get a full activation key to your computers and forget about us forever.
Victim: ok, I need to get with out team when they're back on Monday to see what we're able to get and send to you
Attacker: On Monday we are waiting.
Victim: What kind of files are we allowed to upload? All we've been able to get are some encrypted log files, will that work?
Attacker: You can select 2-3 random files from the list, and we will upload them to this chat as proof of availability. To prove that we can decrypt your data correctly, you can upload 2-3 encrypted files to our chat, and we will upload the decrypted copies back
Victim: Please decrypt the following files:
Victim: [redacted] (0.555 MB)
Victim: [redacted] (0.238 MB)
Victim: [redacted] (0.239 MB)
Attacker: [redacted].log (0.551 MB)
Attacker: [redacted].log (0.234 MB)
Attacker: [redacted].log (0.234 MB)
Victim: Thank you. We are considering your demands, is there any way you could provide a discount to your price?
Attacker: As a sign of goodwill and quick closing of the deal, we are ready to give a 10% discount and stop at the price of 63,000 dollars. You can pay this amount as we have reviewed your financials. Talk to the management and pay, after payment you will get everything you agreed on.
Victim: Understood. If we only require either the decryptor or confidentiality, would the cost be adjusted accordingly?
Attacker: Understand that we don’t have something that requires you to pay separately for something. Any payment includes all our terms and conditions. It depends whether you need decryption or not. Should your data be deleted or not, etc. Everything is included in the complex. Hurry up, there is very little time left.
Victim: That makes sense. We have some key decision makers that are flying in to discuss your deal. We expect to have an update for you early next week.
Attacker: As we see that you are interested in making a deal as soon as possible, we do for you an exception and extend the timer till the 19th of February for you to make a decision with your management and inform us about the payment. Please, don't delay with it, otherwise we will return with the tools which are stronger. You must understand that as the timer will expire we will post your files on our blog.
Victim: Our apologies, we are awaiting a decision from leadership. Can we have one more day to consider your offer?
Attacker: we extended the timer for 24 hours.
Attacker: So you just had a meeting about finances. What do you have to offer? We are willing to make an additional discount and accept payment from you today. The price will be 60,000 dollars. That's a very good discount. We're ready to make the deal today and start rebuilding you. It's up to you. Time is running out today.
Attacker: We see that you are not interested in the security of your patients and choose to play the silent way. Tommorow we will publish a press relise about you on our blog, and in a couple more days all of your data will become public. You still have time to start collaborating and do it without any attention from the press and the public.
Attacker: http://ijzn3sicrcy7guixkzjkib4ukbiilwc3xhnmby4mcbccnsd7j2rekvqd.onion/site/view?uuid=[redacted]